Internet of Things: A 360 Degree Overview
The Internet of Things (IoT) is a great, disruptive power and the basis for digital companies which has merged the digital and physical worlds.
Undoubtedly, IT leaders need to deliver the new enterprise IoT solution as they have faced the growing pressure from business solutions where improving the operational efficiency was a major concern. The real value of enterprise IoT solution comes when an insight into data is given and hence it is made more optimized by combining the sensor data, data from enterprise systems like ERP, CRM, and PLM etc. There are 5 steps to a cognitive IoT application development process.
WHAT AN IOT SOLUTION LOOKS LIKE?
Although there is a wide range of diversity, there is also a commonality that can illustrate the anatomy of IoT solutions. Let’s see the layered approach of an IoT product development which describes the anatomy of IoT identifying the relevant services:
IOT ENDPOINTS:
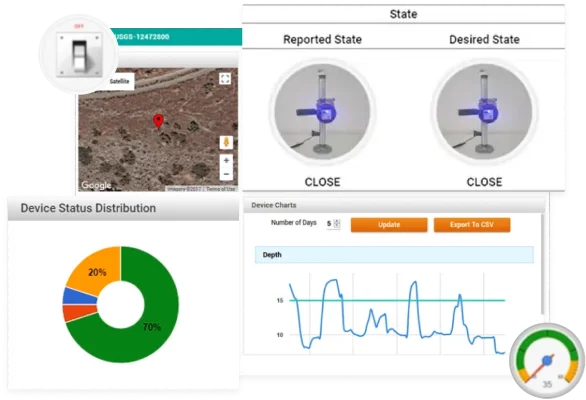
This is the most important layer when an IoT solution provider is developing the IoT platform as it has the physical equipment and the operational technology which connect and communicate things.
- Sensors: IoT sensors monitor the temperature, pressure, motion etc. and are mounted within to collect and report data on the real-time action of the devices.
- Actuators: Controls the logical or physical condition of a product through signs they get from IoT programs or other programs, such as opening a valve, or turning a camera, either engine or mild emitting. This includes the commands and controls delivered to embedded software e.g. to update or reboot configurations.
- Things/Equipment: Endpoints in IoT are the things that are connected with each other whether they are cars, jet engines or lightning systems.
- Edge Computing Device: The complete and distributed architecture helps in the data processing at the edge of the network. Load on the network is detected when a large amount of data is transmitted over a network. Therefore, in some cases, the data is communicated to the cloud based on preferences.
- Device Communication: Whenever the IoT device communicates, the physical layer and the protocols used are distinguished apart. Depending on the use case; the gateways, mesh networks, direct/broadcast services, mobile devices are used to communicate the physical layer. The choice for the physical layer will determine which communication protocols are most suitable (e.g. MQTT, COAP, HPPT(S), AMQP, ZigBee, Z-Wave, etc.)
- Mediators/Agents: Agents are the components that mediate between a set of IoT devices and bridges the gap between the sensors and the cloud. The agents also decide which data to send and when. Also, they process the updates and the commands coming from the cloud.

IOT SOFTWARE:
The next layer that comes is the cloud platform which brings important IoT development services together and manages the IoT endpoints securely.
- Device Management: Enterprise IoT solution has simplified the process of operating the endpoint devices. It has made the monitoring, testing, and troubleshooting of the connected devices much easier.
- Event and Data processing: In event and data processing, the data stream comes from various connected devices like filtering and monitoring devices which are used for
- Analytics/Machine learning: Machine learning and analytics services perform a statistical analysis which helps in detecting the patterns on a device for predictive maintenance and triggering engineering changes.
- API Management: It is the most flexible layer provided by an IoT solution Provider such that the devices can communicate properly and can integrate the backend services.
- Security Management: It ensures that the IoT endpoints do not get exposed to security threats. The sensitive information generated by IoT devices are vulnerable to hacks and damages. The IoT Development Security services include network connectivity, authentication, and data loss prevention which keep the IoT software secured.
IOT APPS:
This is the layer where data is turned into actionable insight, a life is brought into the IoT solutions and IoT solution is put in the hands of business users. An integration with back-end and third-party services are established at this layer and also proper workflows are defined to give an insight into the IoT solution.
The following core services illustrate the App Layer in IoT Solution Provider:
- Integrated Development Environment (IDE):A sufficient time for designing the IoT Apps is required. The IDE can be a traditional one or a specific model is driven for collaborative and visual development of the IoT App. To create the build and application packages, core services for the configuration of software and merging are required. The IDE guide the IoT developers to apply the right patterns and best practices for IoT Development Services.
- Multi-Channel Apps: In today’s world of Mobile Application, the IDE ideally supports developing an IoT Application on cross-platform which is optimized for specific factors and supports gestures with minimal overhead.
- Integration:Integration is the lifeblood of IoT Product Development. The Apps gets access to IoT endpoints for tracking the full history of any asset after receiving an alert. Various IoT development software services like Machine learning algorithms, time series data are weaved into IoT Apps. Not only this but the integration with enterprise back-ends and third-party services helps in the proper workflow and making IoT apps contextual.
- Testing: Testing and Quality Assurance are the most essential disciplines in IoT product Development. Testing on various stages like Unit testing, Integration, and Functional helps in minimizing the test burden relative to development cycles.
- Deployment:To efficiently manage the IoT apps, staged deployment helps to target environments and automated provisioning of application resources. Ideally, you can deploy the App on a cloud of your choice.
- Management:For proficient management of the IoT Apps, User Management and application management are highly important for horizontal/vertical scaling and high-configuration.
- Security:Security plays a vital role in the IoT Product Development. The runtime environment and the security settings like access and authentication are highly important in the security of IoT Apps.
 info@biz4group.com
info@biz4group.com